Install rsyslog on Alpine
The Adiscon Alpine Repository supports recent rsyslog versions for Alpine Linux including necessary third party packages.
To install rsyslog on Alpine, simply execute the following commands as root from the commandline:
cd /etc/apk/keys wget http://alpine.adiscon.com/rsyslog@lists.adiscon.com-5a55e598.rsa.pub echo 'http://alpine.adiscon.com/3.7/stable' >> /etc/apk/repositories apk update apk add rsyslog
Questions? Suggestions? Bug Reports? Provide it here: https://github.com/rsyslog/rsyslog-pkg-alpine/issues Feedback is appreciated!
Installing rsyslog from RPM
We want to describe here, how to install rsyslog from the RPM repository on RHEL/CentOS 5 and 6. Currently, we have RPMs available for the most recent versions of rsyslog.
To use the repository, please follow these steps.
1. Obtain the .repo file
To be able to use the RPM repository, you need a .repo file. Using your webbrowser, go to http://rpms.adiscon.com. Here, either download the rsyslogall.repo file or go to the subfolder for the desired version (e.g. v7-stable) and download the rsyslog.repo file from there.
2. Placing the file in the correct location
You now need to place the downloaded file in the correct folder. The .repo file must be placed in
/etc/yum.repos.d/
3. Finding updates
You should now do a “yum update”. The update for rsyslog will be detected automatically. Note, that the file rsyslogall.repo contains the repository configuration for each available branch, whereas the rsyslog.repo only provides repository configuration for the selected branch.
A note on signed RPM’s
On RHEL/CentOS 5 it is not possible to check for signed RPM’s. This is due to a bug in the RPM/YUM subsystem. So, Please DO NOT USE gpgcheck=1! If you however couldn’t resist trying it, and your system stucks with “Header V3 RSA/SHA1 signature: BAD, key ID e00b8985″, follow these steps:
- Set gpgcheck in your rsyslog.repo file back to 0.
- Run this command to remove the gpg key from your system: rpm –erase gpg-pubkey-e00b8985-512dde96
Install rsyslog on Ubuntu
The Adiscon Ubuntu Repository has been setup to provide the latest rsyslog versions on Ubuntu including necessary third party packages.
We support those Ubuntu versions that have not yet reached end of life as of Ubuntu policy. For some Ubuntu versions beyond end of life, we may have packages in the PPA, but these may disappear at any instant and are not supported at all.
An overview of the currently available packages can be found here: Launchpad PPA
To install rsyslog on Ubuntu execute this from a terminal window:
sudo add-apt-repository ppa:adiscon/v8-devel sudo apt-get update sudo apt-get install rsyslog
Packages for debug symbols:
Open file: /etc/apt/sources.list.d/adiscon-ubuntu-v8-devel-xenial.list Edit first line to: deb http://ppa.launchpad.net/adiscon/v8-devel/ubuntu xenial main/debug sudo apt-get update sudo apt-get install rsyslog-dbgsym
If you prefer to run the scheduled stable build use:
sudo add-apt-repository ppa:adiscon/v8-stable sudo apt-get update sudo apt-get install rsyslog
Note: the scheduled stable build is cut every 6 weeks from the daily stable build.
Questions? Suggestions? Bug Reports? Provide it here: https://github.com/rsyslog/rsyslog-pkg-ubuntu/issues Feedback is appreciated!
The following short video shows how the steps are actually done:
Install rsyslog on RHEL/CENTOS


The Adiscon RPM Repository supports recent rsyslog versions for RHEL/CentOS 7, 8 and 9 including third party packages.
Using the daily stable build
Packages for rsyslog’s daily stable are created every night and updated at 01:00 am CET.
Note: The daily repository usually at least as stable as v8-stable, because it has the latest fixes.
To install the daily stable on CentOS, simply execute the following commands as root from command line:
cd /etc/yum.repos.d/
wget http://rpms.adiscon.com/v8-stable/rsyslog.repo # for CentOS 7,8,9
wget http://rpms.adiscon.com/v8-stable-daily/rsyslog-daily.repo # for CentOS 7,8,9
yum install rsyslogTo install the daily stable on RHEL, simply execute the following commands as root from command line:
cd /etc/yum.repos.d/
wget http://rpms.adiscon.com/v8-stable/rsyslog-rhel.repo # for RHEL 7,8,9
wget http://rpms.adiscon.com/v8-stable-daily/rsyslog-daily-rhel.repo # for RHEL 7,8,9
yum install rsyslogThe following video explains the process, including of how to go back the the stock version (if you just want to give our repository a try):
Please accept YouTube cookies to play this video. By accepting you will be accessing content from YouTube, a service provided by an external third party.
If you accept this notice, your choice will be saved and the page will refresh.
Using scheduled stable build
To install the stable on CentOS, simply execute the following commands as root from command line:
cd /etc/yum.repos.d/
wget http://rpms.adiscon.com/v8-stable/rsyslog.repo # for CentOS 7,8,9
yum install rsyslogTo install the stable on RHEL, simply execute the following commands as root from command line:
cd /etc/yum.repos.d/
wget http://rpms.adiscon.com/v8-stable/rsyslog-rhel.repo # for RHEL 7,8,9
yum install rsyslogNote: the scheduled stable release may contain bugs already fixed in the daily stable releases. It is primarily meant for situations where infrequent package updates are desired.
Problems during the installation
Some users experiencing problems at the installation because of a incorrect resolution variable. So please try this first. Open the repofile and replace the variable “$releasever” in the third line through your operating system. Below you can find a example for RHEL7.
The line should looks like this before:
baseurl=http://rpms.adiscon.com/v8-stable/epel-$releasever/$basearch
After the change the line should look like this:
baseurl=http://rpms.adiscon.com/v8-stable/epel-7/$basearch
GPG Key for validation:
—–BEGIN PGP PUBLIC KEY BLOCK—–
mQINBGPqPv8BEAC8grHFvJRSV8OGmRU/t7iMKqfR/uAIiF0ho10p3JLCOJkut0Er
Bm7S0EKON2955yFCrs9q5Zbw1FJS0k1m/++UG6FBsA5e3jkLEctx3qO9A/phvVPe
TqYi3Hjd4OLKYda0Bdx1Z7RnxOWpqvKhtWPO4Uc2vk89VlNgJNFHjw6WbHDAlMc9
hDxWhM7AUQXTJdr8ywkETeQxwKdWzjqS2HKs3ZCoGUsHF83r+kTsIivg9hkUvzOb
tKKmWbdC+ZHKaXtmq89xMesG+HgehuQHHXp4lYx2DhBGxwd0dC/Ew5y3K8Se+m8v
B/X9jY/L4IXdvBAyTV2erSRy+YGraviTaTD1W2llN0GDhG7mtyIFkyWoDgPmVtdE
U32RsDUQ9PK4hKHpqJXquM/DZbk9EjP3grpUifzjrED08oRBnaykGOwHul4BEiDh
Dkd1nkqibS3kj989rdLvS36uP+apn2ccsUYNoci6TIduuEIGqx1kpHizEGMny/Vm
oA1t3KXKruEImzfC5tqbxJQzDnAEcFwC4Fvg/hrFuWuSBuRqB+bvazvUxkTnCFRK
5CVSqUzVhUqXqVgwywcYVJMIKysueFFATUi76alracPo+HtNjsYEjfkLkqPhjfj/
GacFKp/0YS3RjcC+boyycHYmAG/9OFR1NeihDfoLZwg7/50fp2+HdgczlwARAQAB
tE9BbmRyZSBMb3JiYWNoIChSUE0gUGFja2FnZSBzaWduaW5nIGtleSBmb3IgcnN5
c2xvZyAyMDIzKSA8YWxvcmJhY2hAYWRpc2Nvbi5jb20+iQJRBBMBCAA7FiEEMUjR
NJc6v1FbL54xaxHVx49n72QFAmPqPv8CGwMFCwkIBwICIgIGFQoJCAsCBBYCAwEC
HgcCF4AACgkQaxHVx49n72Qp9A/+Lqo8/wmWPcJV9/sFTmobBhHL2E7n7ZEcxY2Y
aFyHwov495gFXFXFyiXKyL/ItA4gBCn5MbX5Oetrs9zSpO5wgfSp67XWIh4FfhfM
79WTrHJkwIosdRr2eH/FSK5lvC5R0xpnSTgDNwG22qR9vO9dqEtN/Skr24KEmjdz
gbC/dlrALOM4Qj4g1TvqOk3cBMwc3GQmOvtvyYa0Dp3kOw/KrBpxW3GVm7Vsxqf1
WpWyOpyisYOghFZyZC/qMcQbwgL1N8pTmOIjJZ3n2AsFts8RKmUcZzVz+I+RGGyJ
eLGXupGb8TUZsp0i7KI0D8XiLFsFkSrVhSFXrtukuOomiUYSEyxRcm/DWO9o5yLF
ZybrLyvPC6T5mdbOxJBc7ZAInMaItR0XznLMIhjzzTx9o4IFmET/SPQ+y35szxVL
To3R70DFvb7dqArs1TrnPRcZjkLbHTr1p0QttVC1SW4NbY8oODiRRAa7ZV143b0p
sv4Gpx9ZQvDrSDGVVRuxdl3KhqdwvaEFDBAjneO2mnV8RawHjRHzayF2js52ZIHd
iVePWNm7wFo6JKThvRt5ewn7xQmUTPwIJS4iWf7TAB/bELAVXP1qQWzin0y6iKh/
ZLLt1gkbBXCEzJCe6K1Krnx0/eInwV9NbUPwXNxC0VIQcShkQUn1E8AEn9tNjThm
P98nqjA=
=UhZe
—–END PGP PUBLIC KEY BLOCK—–
Questions? Suggestions? Bug Reports? Provide it here: https://github.com/rsyslog/rsyslog-pkg-rhel-centos/issues Feedback is appreciated!
Install locations for rsyslog
Not everyone uses the same linux distributions. If Linux at all. And some distributions store files different than others. When building a test environment, we stumbled upon the problem, that if we tried the usual know method
./configure --libdir=/lib --sbindir=/sbin
rsyslog won’t work. Even if there is already rsyslog installed, but we want to use a different version, we will be helpless. Therefore we want to collect a list of different distributions and the different installation paths.
All paths are for 32-Bit operating systems!
Fedora
libdir=/lib sbindir=/sbin
Ubuntu
libdir=/lib sbindir=/usr/sbin
CentOS
libdir=/lib sbindir=/sbin
Debian
libdir=/lib sbindir=/usr/sbin
If you know of other distributions and the install directories, please send us a notification via the mailing list, so we can add it here.
Installing RSyslog 5 on RHEL 4 / 5
To have rsyslog working correctly on RHEL 4 or 5, some conditions have to be met. The method described has been tested with rsyslog 5.7.1.
First of all compile and install the dependencies.
- gnutls-2.8.6.tar.bz2
- libgcrypt-1.4.6.tar.gz
- libgpg-error-1.9.tar.gz
- libtasn1-2.2.tar.gz
After that, you can install rsyslog using the following commands:
./configure PKG_CONFIG_PATH=/usr/local/lib/pkgconfig --enable-gnutls make make install
It could happen, that the install might complain about gnutls.pc. Simply comment out the URL found near the start of the file /usr/local/lib/pkgconfig/gnutls.pc.
Credit for this find goes to Forum member Johann Reinhard (johannreinhard).
What rsyslog is today: a high-performance log ingestion and ETL engine
The site title and GitHub project tagline now describe rsyslog as a high-performance log ingestion and ETL engine.
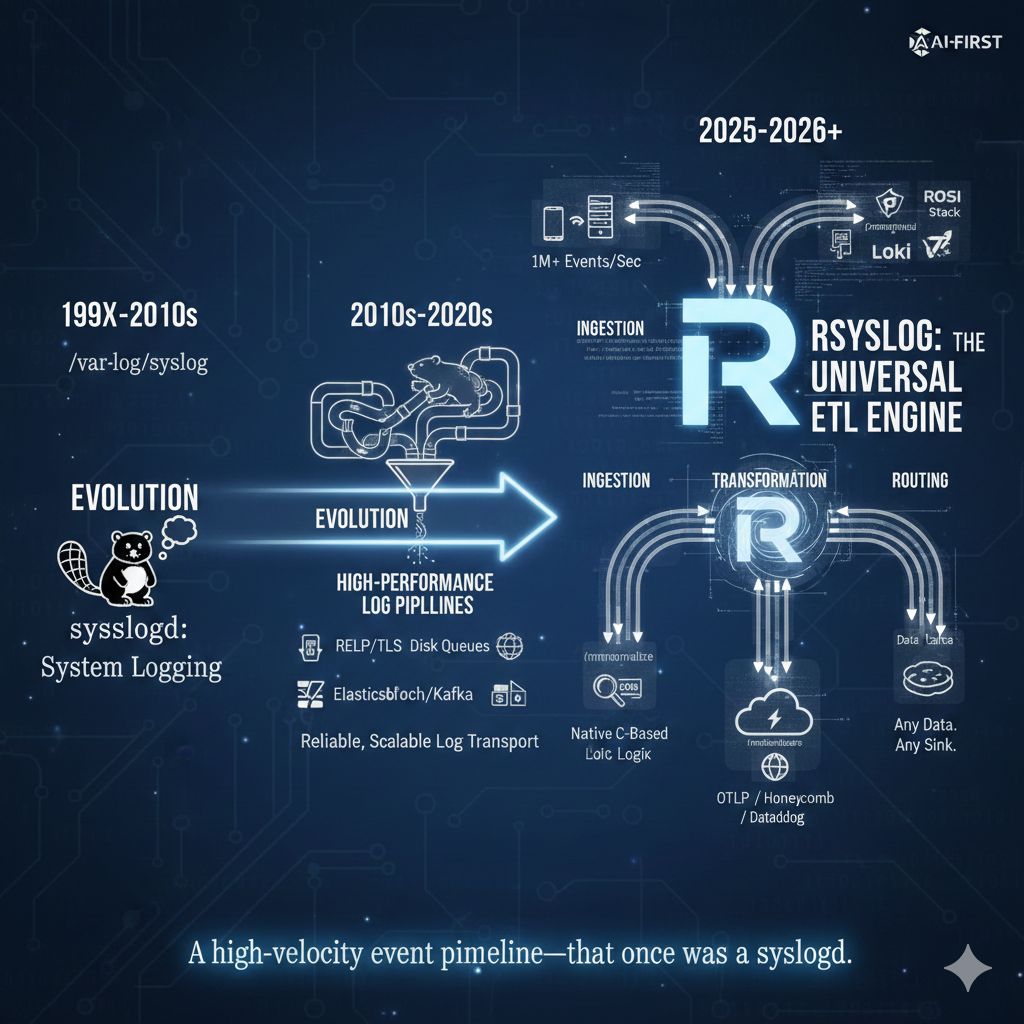
This is a small but visible change. It reflects how rsyslog is actually used today in modern infrastructures, and it aligns the project’s public description with long-standing technical reality. It is not a rebranding exercise, and it does not change what rsyslog is compatible with or where it comes from.
If you have followed the project for a long time, the wording may stand out. That is intentional. It acknowledges an evolution that has been underway for years and that many users already rely on in production.
Continue reading “What rsyslog is today: a high-performance log ingestion and ETL engine”imfile inotify handling improved: safer systems, lower rsyslog impact
Large imfile deployments can put pressure on Linux inotify resources. In practice, running out of inotify watches is very uncommon, but when it does happen, the consequences used to be unpleasant and system-wide.
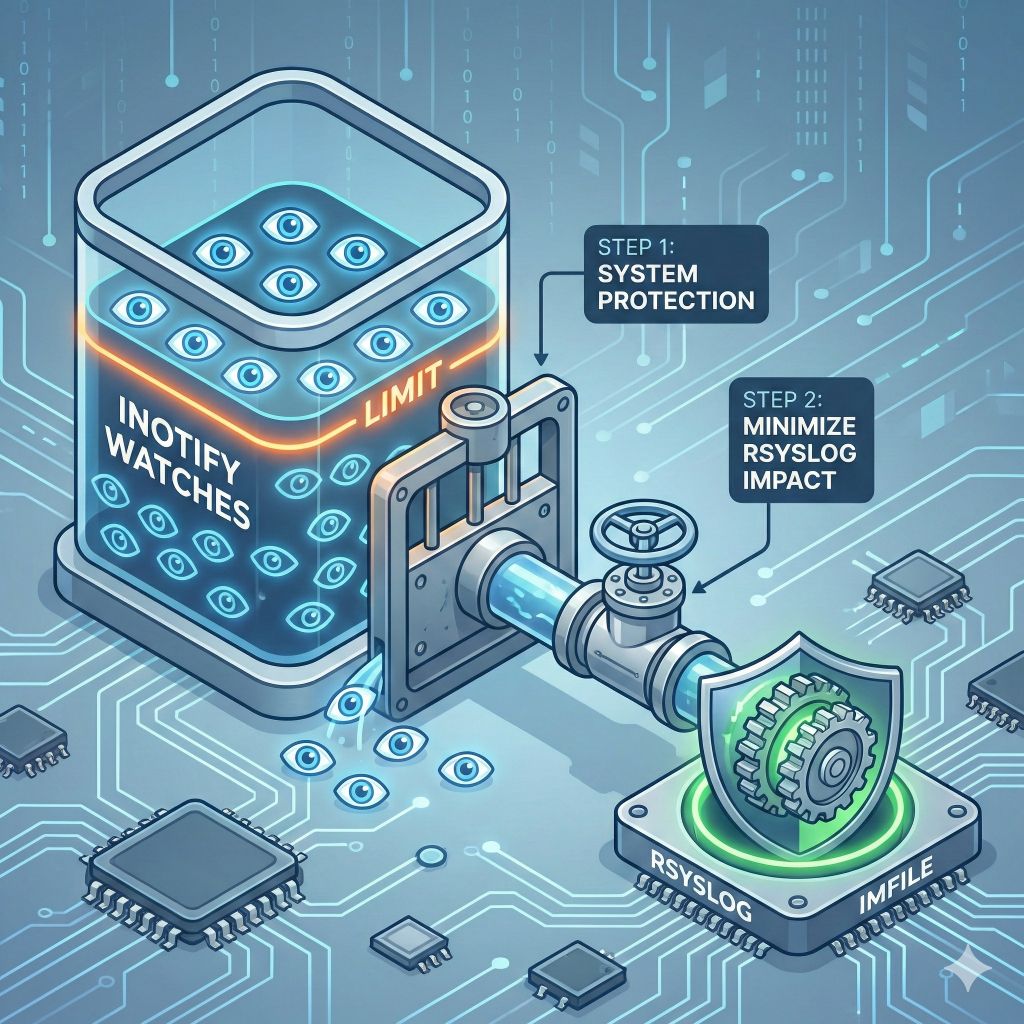
To address this properly, we completed a single improvement delivered in two steps: treat inotify usage as a bounded, shared system resource while keeping rsyslog itself as unaffected as possible.
Continue reading “imfile inotify handling improved: safer systems, lower rsyslog impact”rsyslog: High-Performance Syslog Server and Log Aggregation Tool
The rocket-fast system for log processing pipelines
rsyslog helps you collect, transform, and route event data reliably at scale. Built for speed, flexibility, and control in modern Linux and container environments.
Runs great on single hosts and in containerized deployments.
Trusted by organizations worldwide
1M+
Messages per second
100+
Input/output modules
20+
Years in production
📦 Current versions
Download the latest stable release, daily builds, or explore containerized deployments. All versions include documentation and release notes.
🪟 Windows Agent: 8.1 [download]
Get started in 60 seconds
Two quick ways to try rsyslog.
# Debian/Ubuntu
sudo apt-get update
sudo apt-get install -y rsyslog
sudo systemctl enable --now rsyslog
# Config lives in /etc/rsyslog.conf and /etc/rsyslog.d/# Docker (example)
docker run --name rsyslog/rsyslog -d \
-v $(pwd)/rsyslog.conf:/etc/rsyslog.conf:ro \
-p 514:514/tcp -p 514:514/udp \
rsyslog/rsyslogSee First steps guide and Basic configuration reference for more detail.
What is rsyslog?
rsyslog is an open-source, high-performance engine for collecting, transforming and routing event data. It ingests from diverse sources (files, journals, syslog, Kafka), applies parsing, enrichment and filtering rules via RainerScript and modules like mmnormalize, buffers safely with disk-assisted queues, and forwards to Elasticsearch, Kafka, HTTP endpoints or files. With over 20 years of proven reliability, rsyslog bridges classic syslog-style logging and modern data pipelines — now guided by an AI-First (human-controlled) vision for smarter observability.
Why operators rely on rsyslog
💾 Reliable delivery
Disk-assisted queues and backpressure controls keep pipelines flowing.
📎 Flexible parsing
Support for regex, structured formats, JSON, and liblognorm pipelines.
📦 Powerful routing
Conditional rules and reusable templates with RainerScript.
📭 Broad outputs
Files, TCP/UDP/TLS syslog, Kafka, HTTP, and database destinations.
📰 Performance at scale
Multi-threaded design with tuning controls for predictable latency.
🌍 Runs anywhere
Bare metal, virtual machines, and containerized environments.
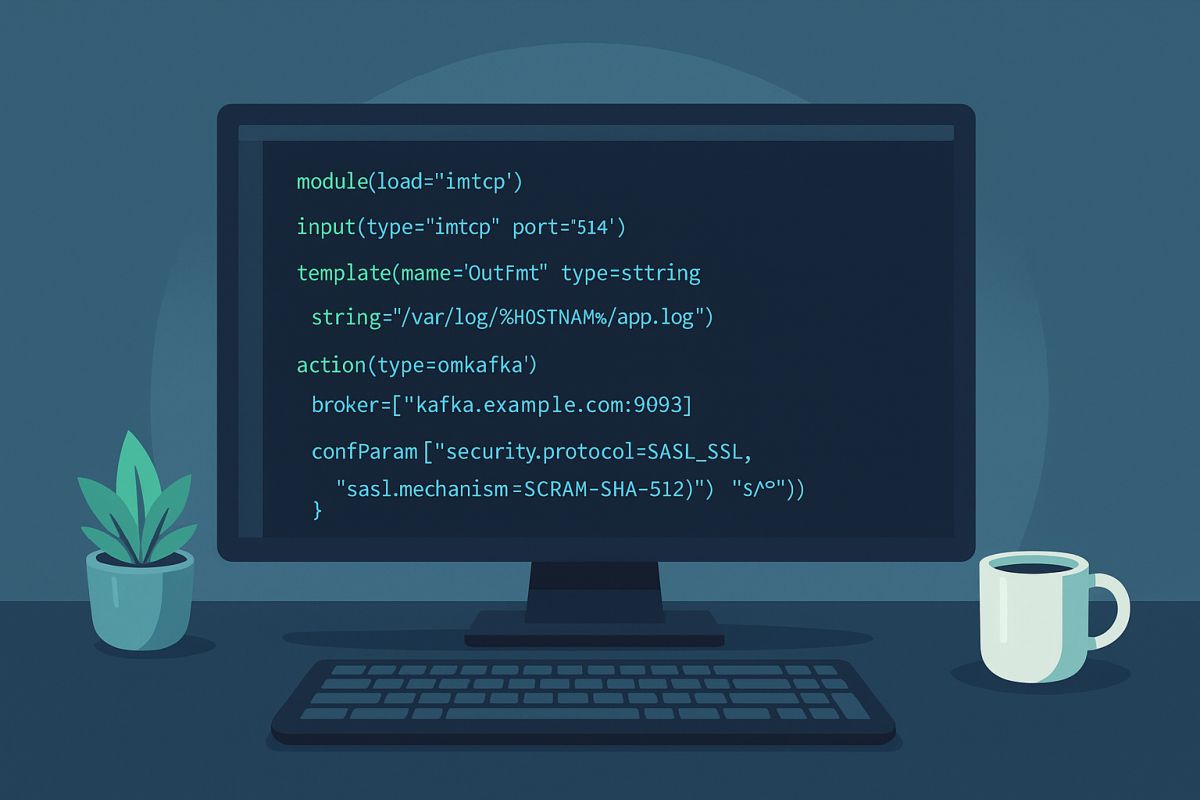
Works with your observability stack
| Target | Description / Docs link |
|---|---|
| Elastic / OpenSearch | output-elasticsearch module guide |
| Grafana Loki | HTTP/JSON shipping example |
| Kafka | omkafka documentation |
| Splunk HEC | omhttp configuration example |
| Files & rotation | omfile output reference |
| Databases | Output modules overview |
Integrates via open protocols (syslog, TCP/TLS, HTTP, Kafka). No cloud-vendor lock-in.
💼 Professional services for production workloads
Need expert help to ship faster and reduce risk? Our team provides architecture reviews, performance tuning, migrations, troubleshooting, and long-term support—tailored to your stack.
- ✅ Architecture & performance reviews
- ✅ Production readiness, HA & DR patterns
- ✅ Migrations (e.g., from Kiwi, Logstash)
- ✅ Custom modules and integrations
- ✅ Incident response and troubleshooting
- ✅ SLAs and long-term support options
💻 Two tiny examples
Example A (RainerScript)
module(load="imuxsock")
module(load="imklog")
template(name="jsonl" type="list") {
constant(value="{\"ts\":\"") property(name="timereported" dateFormat="rfc3339")
constant(value="\",\"host\":\"") property(name="hostname")
constant(value="\",\"msg\":\"") property(name="msg" format="json")
constant(value="\"}\n")
}
*.* action(type="omfile" file="/var/log/events.jsonl" template="jsonl")Example B (RainerScript)
module(load="imuxsock")
module(load="omkafka")
if ($programname == "sshd") then {
action(type="omkafka"
broker=["kafka:9092"]
topic="security-auth"
template="RSYSLOG_TraditionalFileFormat")
}🤖 Self-support with the rsyslog Assistant
The rsyslog Assistant is an AI-powered self-support tool based on curated, verified project knowledge, supervised by maintainers. Use it to explore configuration options, examples, and troubleshooting tips.
📢 Latest from the project
The rsyslog Evolution: Bridging BSD Heritage with Adiscon Innovation
It is a well-documented fact in the open-source community that rsyslog traces its lineage back to the original 1980s BSD…
Docs moved to new Domain
We have today moved the rsyslog official documentation to https://docs.rsyslog.com/doc instead of our long-standing location directly on www.rsyslog.com/doc. All existing…
rsyslog 8.2602.0: ROSI Collector, rate-limit policies, stronger TLS, and telemetry integration
We have released rsyslog 8.2602.0, the February 2026 scheduled-stable version. Scheduled-stable releases are bi-monthly snapshots of the daily-stable branch, providing…
rsyslog 8.2510.0 (2025.10) released
We have today released the 8.25100 rsyslog scheduled stable release. This release delivers three main themes: better Windows Security event ingestion, more flexible JSON handling end to end, and pragmatic compatibility fixes across popular outputs and platforms. It also includes steady documentation improvements and CI hardening.
Continue reading “rsyslog 8.2510.0 (2025.10) released”

