rsyslog 5.9.4 (v5-devel)
Download file name: rsyslog 5.9.4 (devel)
rsyslog 5.9.4 (devel)
md5sum: 408f59536a10f34a73e3af000ca81639
Author: Rainer Gerhards (rgerhards@adiscon.com)
Version: 5.9.4 File size: 2.382 MB
rsyslog 5.9.4 (devel) released
This release provides support for “trusted properties”, which may enhance overall system security. This is a new concept and feedback on it is appreciated. For more details on trusted properties, please visit
http://www.rsyslog.com/what-are-trusted-properties/
or Rainer’s blog post with some more background about trusted properties:
http://blog.gerhards.net/2011/11/trusted-properties-in-rsyslog.html
In addition to this feature, we have reduced dependency on libgcrypt and fixed some bugs.
ChangeLog:
http://www.rsyslog.com/changelog-for-5-9-4-v5-devel/
Download:
http://www.rsyslog.com/rsyslog-5-9-4-devel/
As always, feedback is appreciated.
Best regards,
Florian Riedl
Changelog for 5.9.4 (v5-devel)
Version 5.9.4 [V5-DEVEL], 2011-11-29
- imuxsock: added capability to “annotate” messages with “trusted information”, which contains some properties obtained from the system and as such is sure to not be faked. This is inspired by the similiar idea introduced in systemd. removed dependency on gcrypt for recently-enough GnuTLS
see: http://bugzilla.adiscon.com/show_bug.cgi?id=289 - bugfix: imuxsock did no longer ignore message-provided timestamp, if so configured (the *default*). Lead to no longer sub-second timestamps.
closes: http://bugzilla.adiscon.com/show_bug.cgi?id=281 - bugfix: omfile returns fatal error code for things that go really wrong previously, RS_RET_RESUME was returned, which lead to a loop inside the rule engine as omfile could not really recover.
- bugfix: rsyslogd -v always said 64 atomics were not present
thanks to mono_matsuko for the patch
What are “Trusted Properties”?
Rsyslog can annotate messages from system log sockets (via imuxsock) with so-called “Trusted Properties”. These are message properties not provided by the logging client application itself, but rather obtained from the system. As such, they can not be faked by the user application and are trusted in this sense. This bases on the similar idea introduced in systemd.
The following trusted properties are available:
| _UID | The userid under which the logging process is being executed. |
| _GID | The group id under which the logging process is being executed. |
| _PID | The PID of the logging process. Note that this PID, if configured, is also put into the syslog tag. |
| _EXE | Path to the binary that is logging |
| _COMM | The name (as visible by top) of the logging process. |
| _EXE | The full command line of the logging process. Note that this string can contain spaces, thus it is always provided in quoted form. |
Property names are deliberately based on property names in the systemd proposal. Additional properties can be added upon request. User- and Group-IDs as well as the PID are obtained via SCM_CREDENTIALS and as such should be always available on a relatively recent Linux system. The other properties are obtained from the /proc virtual file system. Note that this can be somewhat racy. Most importantly, these properties can not be obtained if the process has already been terminated when the message is being processed by rsyslogd. This can occur for very quick processes (logger being a prime example) and has happened in practice (for the same reason, it is theoretical possible that invalid information is reported, if the PID are reused extremely quickly – this is so unlikely we did not care about this case).
All annotations are currently (Nov 2011) placed at the end of the message, starting with ” @[” (the first character being a space). The annotation is ended with “]”. This is done to keep consistent with legacy syslog implementations. However, the format will probably changed and is intended to be moved over to a RFC5424 structured data item. Also, the property names were currently chosen for best fit with systemd. As systemd does not follow the relevant standards, we may at later time change to standard names, once they become fully available. So please be prepared for some future change if you begin to use this feature. You may guess that we will preserve legacy format when doing changes, but we do not promise that ;)
A sample of a message with trusted properties looks as follows:
2011-11-29T16:57:13.634852+01:00 testhost su: pam_unix(su-l:session): session opened for user root by examp(uid=677) @[_PID=5933 _UID=0 _GID=677 _COMM=su _EXE=/bin/su _CMDLINE="su - "]
The annotation is given in boldface. Note that this is all on one line. It is broken across several lines just for readability.
This feature is available starting with version 5.9.4 in the v5 rsyslog branches.
First Impression of Journald
We got a couple of questions on the planned new logging system that shall come with systemd. Rainer Gerhards, rsyslog’s development lead, has taken a quick look at journald and posted about his first impression. Have a look at his blog post journal and rsyslog if you are interested in how we think rsyslog is affected. In the mean time, there is also a description of why we think journald’s log chaining is simply broken and conveys a false sense of security.
How to setup rsyslog to get Event Logs from a second maschine
The Article is applicable to all versions of EventReporter, MonitorWare Agent and rsyslog.
1. Configure EventReporter with a Service “Eventlog Monitor Service”.
Attention if you use Windows Vista or Windows 7 skip to step 1.2.
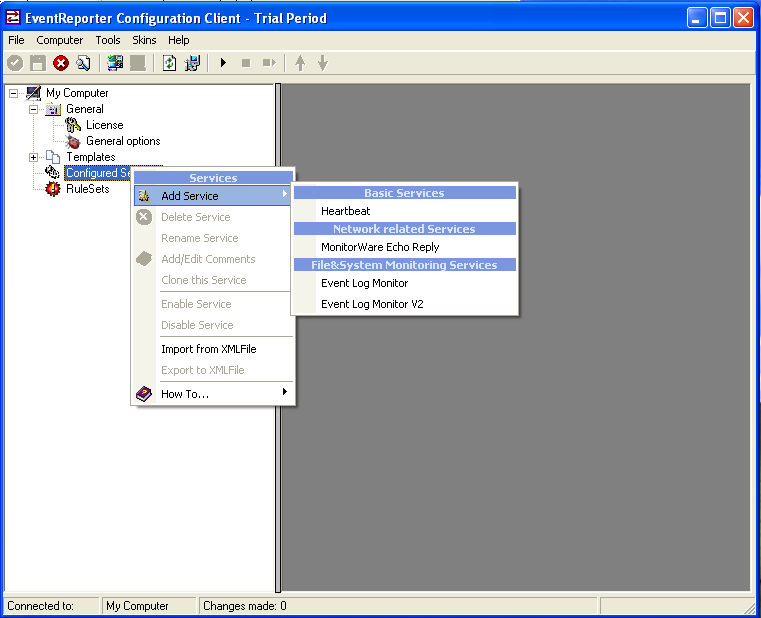
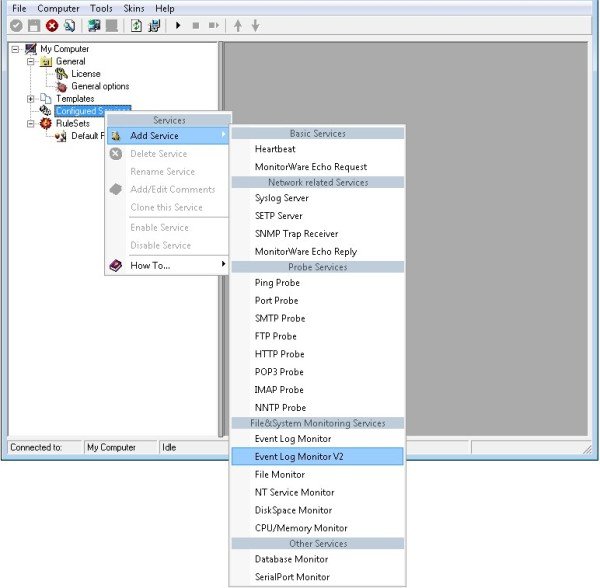
First, right click on “Services”, then select “Add Service” and then “Event Log Monitor”:
Once you have done so, a new wizard starts.
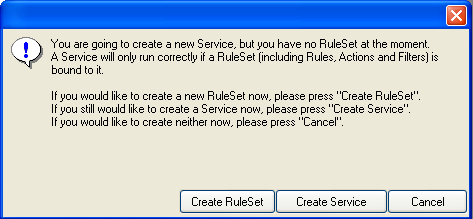
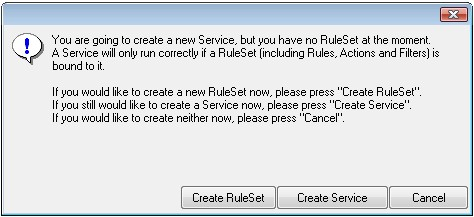
If the following Pop-up appears, please select “Create Service”:
Again, you can use either the default name or any one you like. We will use “My Event Log Monitor” in this sample. Leave the “Use default settings” selected and press “Next”.
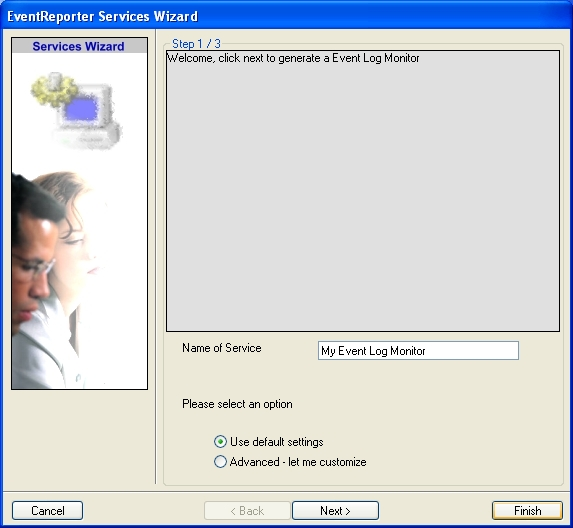
As we have used the default, the wizard will immediately proceed with step 3, the confirmation page. Press “Finish” to create the service. The wizard completes and returns to the configuration client.
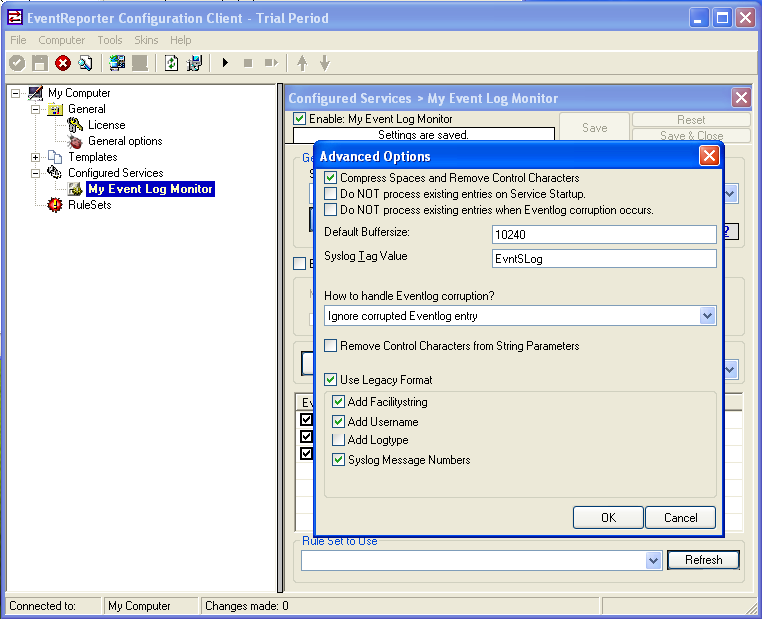
Now, you will see the newly created service beneath the “Services” part of the tree view. To check its parameters, select it. Click on Advanced Options then select “Use Legacy Format” :
1.2 Configure EventReporter with a Service “Eventlog Monitor Service 2”.
Note: This guide explains how to set up the EventLog Monitor Service for Windows Vista. These steps are not applicable if you are using Windows XP.
First, right click on “Services”, then select “Add Service” and then “Event Log Monitor V2”:
Once you have done so, a new wizard starts.
If the following Popup appears, please select “Create Service”:
Again, you can use either the default name or any one you like. We will use the default name in this sample. Leave the “Use default settings” selected and press “Next”.
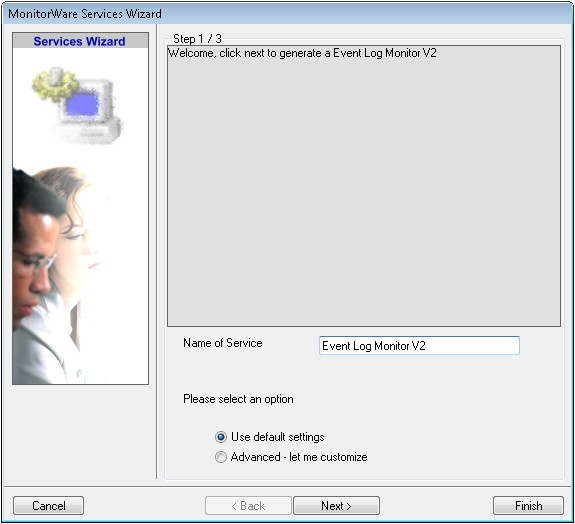
As we have used the default, the wizard will immediately proceed with step 3, the confirmation page. Press “Finish” to create the service. The wizard completes and returns to the configuration client.
Now, you will see the newly created service beneath the “Services” as part of the tree view. To check its parameters, select it:
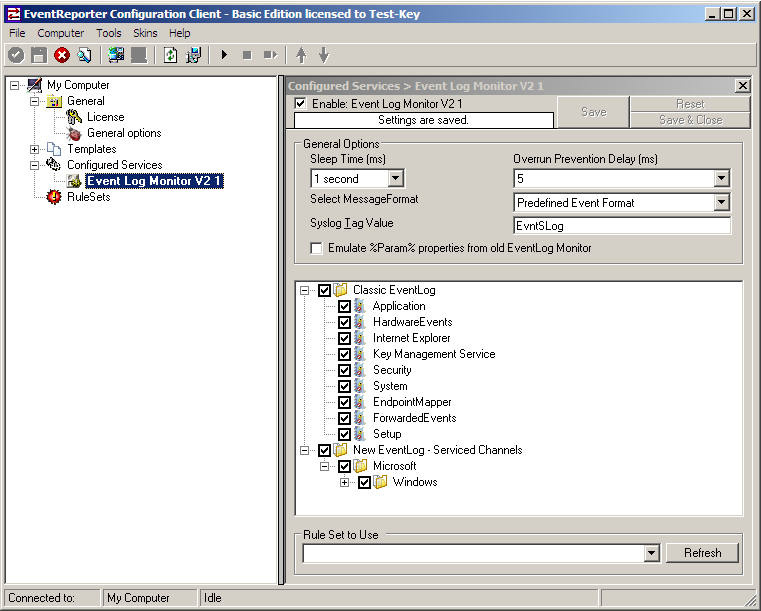
As you can see, the service has been created with the default parameters.
2. Add a “Forward via Syslog” Action.
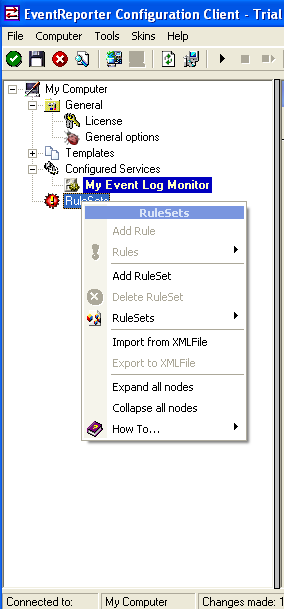
First we define a new rule set. Right-click “Rules”. A popup menu will appear. Select “Add Rule Set” from this menu. On screen, it looks as follows:
Then, a wizard starts. Change the name of the rule to whatever name you like. We will use “Forward syslog” in this example. The screen looks as follow:
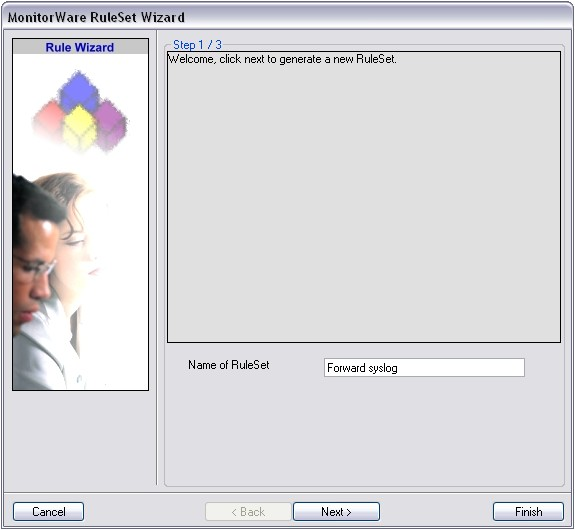
Click “Next” to go on with the next step.
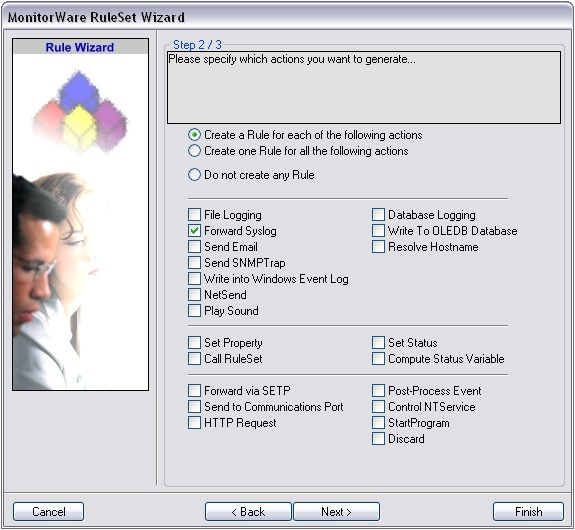
Select only Forward via Syslog. Do not select any other options for this sample. Also, leave the “Create a Rule for each of the following actions” setting selected. Click “Next”. You will see a confirmation page. Click “Finish” to create the rule set.
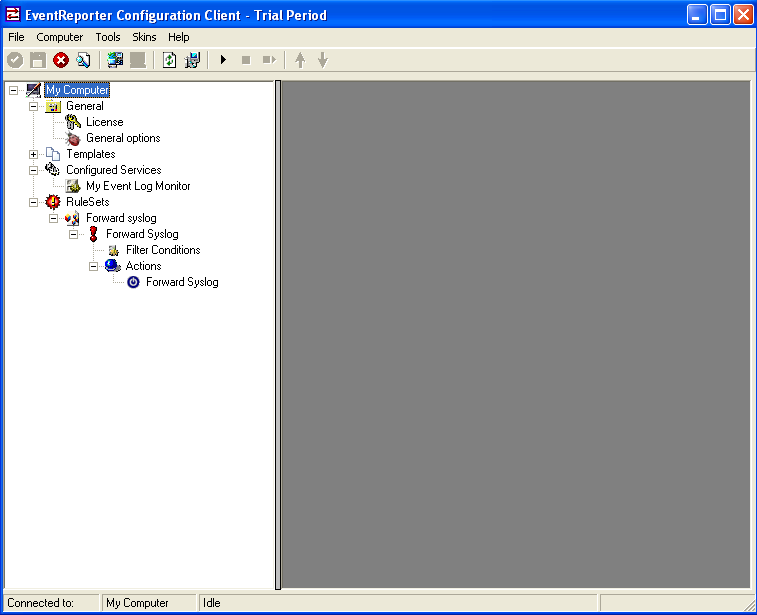
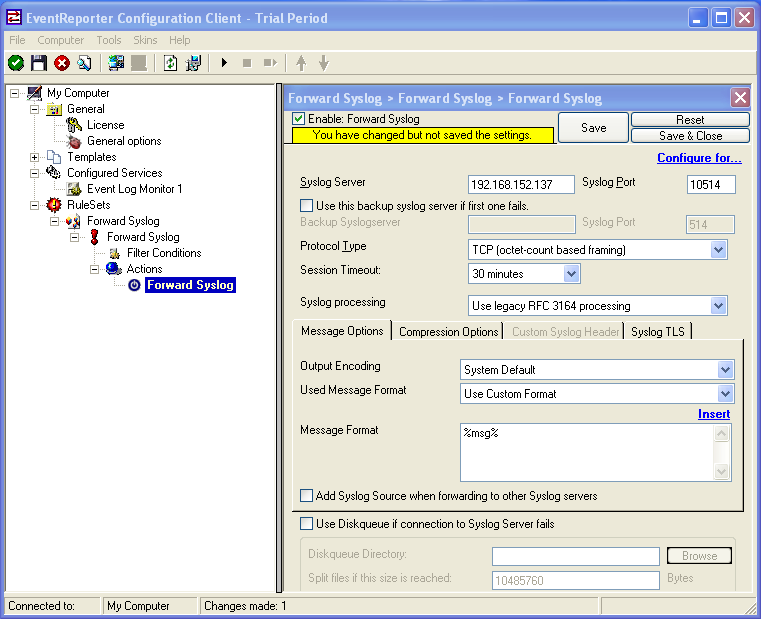
As you can see, the new Rule Set “Forward syslog” is present. Please expand it in the tree view until the action level of the “Forward syslog” Rule and select the “Forward syslog” action to configure.
3. Configure the “Forward via Syslog” Action.
Now, we are going to configure the necessary settings for forwarding via syslog. Type the IP or the hostname of your syslog server into the Syslog Server field in the form. Then Change the protocol to “TCP (octet-count based framing”. We use TCP that we will have no traffic lost. And edit the Port to 10514. Attention EventReporter and rsyslog must use the same port and the same protocol.
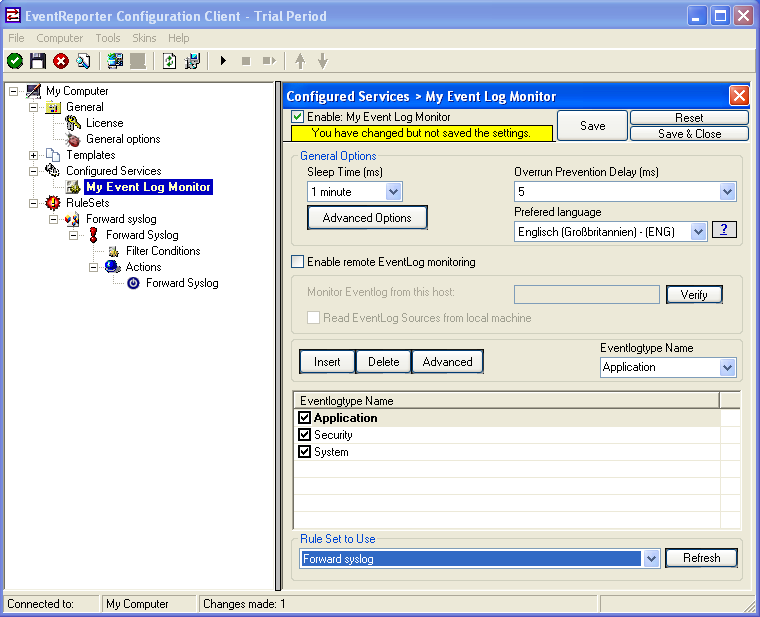
4. Configure Event Log Monitor which Rule to use.
Then Left-Click on Event Log Monitor then change “Rule Set to Use” to your Rule set. On the screen, it looks as follows:
5. Setup rsyslog for TCP reception
Now, we are going to configure the necessary settings for the TCP reception. Because EventReporter forward via syslog over a TCP connection so rsyslog must reception TCP.
Then open the rsyslog configuration. The normal path is “/etc/rsyslog.conf” and copy and paste this code into the Configuration.
Use this code for the TCP Syslog reception:
# Provides TCP Syslog reception
$ModLoad imtcp.so
$InputTCPServerRun 10514
If you use a UPD connection then use this code:
# Provides UDP syslog reception
$ModLoad imudp.so
$UDPServerRun 10514
Please restart rsyslog afterwards.
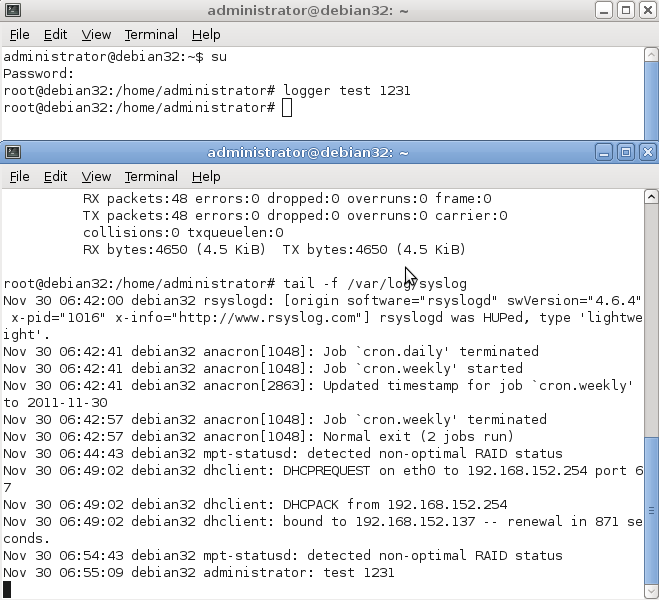
6. Test rsyslog
First switch to your Unix machine then open a new command prompt under Unix then type “tail -f /var/log/syslog”. With this command you now see all log messages which rsyslog receive.
Then open a new command prompt and write “logger test 1231”. Then you must see the message in the first command prompt.
On the screen, it looks as follows:
7. Verifying the configuration of rsyslog and EventReporter
First open a new command prompt under Unix then type “tail -f /var/log/syslog”.
Then switch to the second machine and start EventReporter. Then switch to your Unix machine and watch the command prompt there you see the incoming “Eventlogs” in the command prompt.
On the screen its look like:
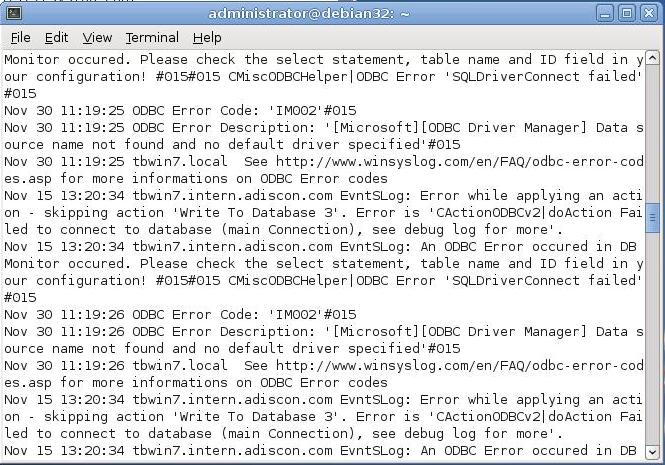
If nothing arrive then check your EventReporter and rsyslog configuration if both use the same port and if both use the same protocol.
That’s it. This is how to receive syslog data from another device.
rsyslog client for Windows
As it currently looks, Adiscon will most probably create a specialised Windows client for rsyslog. This will be based on Adiscon’s MonitorWare technology and provide excellent and high speed integration of Windows clients into a rsyslog infrastructure. While the idea has somewhat matured, we are currently thinking about the details. Expect more information as discussions progress!
In the mean time, you may want to have a look at Adiscon’s EventReporter, which provides excellent Windows-to-rsyslog event log forwarding.
rsyslog 5.8.6 (v5-stable)
Download file name: rsyslog 5.8.6 (stable)
rsyslog 5.8.6 (stable)
md5sum: c46db0496066b82faf735bd4222208d7
Author: Rainer Gerhards (rgerhards@adiscon.com)
Version: 5.8.6 File size: 2.373 MB
rsyslog 5.8.6 (v5-stable) released
This is a maintenance release offering bug fixes. For example for a small bug in property-based filter and a fix for $ActionExecOnlyOnce and more .For more detailed information, please read the changelog.
ChangeLog:
http://www.rsyslog.com/changelog-for-5-8-6-v5-stable/
Download:
http://www.rsyslog.com/rsyslog-5-8-6-v5-stable/
As always, feedback is appreciated.
Best regards,
Tim Eifler
Sending messages with tags larger than 32 characters
The relevant syslog RFCs 3164 and 5424 limit the syslog tag to 32 characters max. Messages with larger tag length are malformed and may be discarded by receivers. Anyhow, some folks sometimes need to send tags longer than permitted.
To do so, a new template must be created and used when sending. The simplest way is to start with the standard forwarding template. The standard templates are hardcoded inside rsyslog. Thus they do not show up in your configuration file (but you can obtain them from the source, of course). In 5.8.6, the forwarding template is defined as follows:
template (name="ForwardFormat" type="string" string="<%PRI%>%TIMESTAMP:::date-rfc3339% %HOSTNAME%
%syslogtag:1:32%%msg:::sp-if-no-1st-sp%%msg%")NOTE: all templates are on one line in rsyslog.conf. They are broken here for readability.
This template is RFC-compliant. Now look at the part in red. It specifies the tag. Note that, via the property replacer, it is restricted to 32 characters (from position 1 to position 32 inclusive). This is what you need to change. To remove the limit … just remove it ;-) This leads to a template like this:
template (name="LongTagForwardFormat" type="string" string="<%PRI%>%TIMESTAMP:::date-rfc3339% %HOSTNAME% %syslogtag%%msg:::sp-if-no-1st-sp%%msg%")
Note that I have renamed the template in order to avoid conflicts with build-in templates. As it is a custom template, it is not hardcoded, so you need to actually configure it in your rsyslog.conf. Then, you need to use that template if you want to send messages to a remote host. This can be done via the usual way. Let’s assume you use legacy plain TCP syslog. Then the line looks as follows:
action(type="omfwd"
Target="server.example.net"
Port="10514"
Protocol="tcp"
Template="LongTagForwardFormat"
)This will bind the forwarding action to the newly defined template. Now tags of any size will be forwarded. Please keep in mind that receivers may have problems with large tags and may truncate them or drop the whole message. So check twice that the receiver handles long tags well.
Rsyslog supports tags to a build-defined maximum. The current (5.8.6) default is 511 characters, but this may be different if you install from a package, use a newer version of rsyslog or use sources obtained from someone else. So double-check.
